Google is one of Palmr's officially supported OIDC providers, offering secure and reliable authentication through Google OAuth 2.0. This integration allows users to sign in to Palmr using their existing Google accounts, providing a seamless single sign-on experience.
Why use Google authentication?
Google authentication provides several advantages for both administrators and users:
- Seamless login experience - Users can access Palmr with their existing Google accounts
- Enhanced security - Leverage Google's robust security infrastructure and two-factor authentication
- Reduced password fatigue - No need to create and remember additional passwords
- Enterprise integration - Perfect for organizations already using Google Workspace
- Automatic user provisioning - New users are created automatically upon first login
Prerequisites
Before configuring Google authentication, ensure you have:
- Google Cloud Console access - Ability to create and manage projects
- Admin privileges in Palmr - Required to configure OIDC settings
- Domain ownership - For production deployments with custom domains
Note: Google is pre-configured as an official provider in Palmr, which means the technical configuration is handled automatically. You only need to provide your OAuth credentials.
Setting up Google Cloud Console
Creating a Google Cloud project
To get started with Google authentication, you'll need to set up a project in Google Cloud Console.
- Navigate to Google Cloud Console: Go to console.cloud.google.com
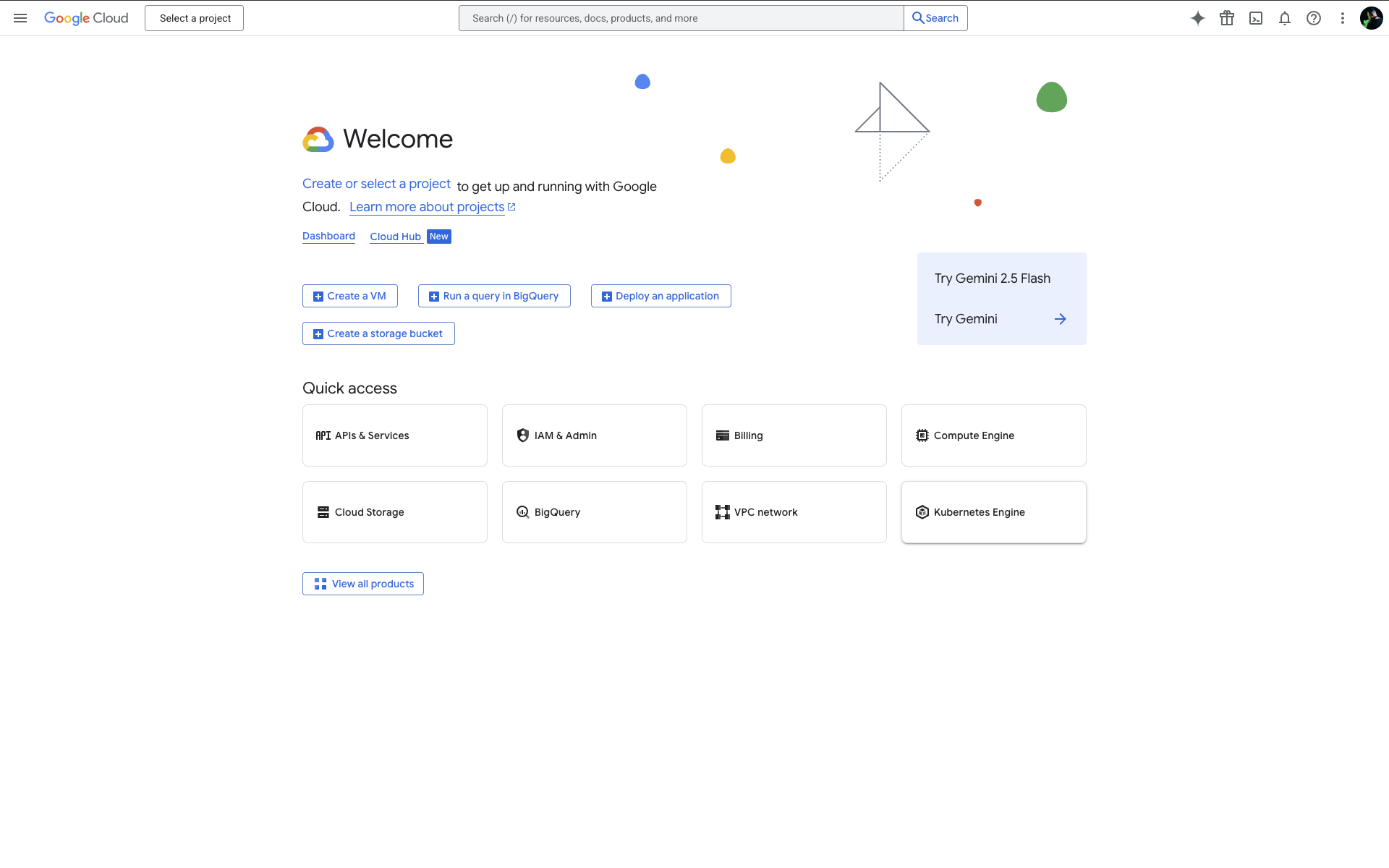
- Create or select a project: Choose an existing project or create a new one for your Palmr installation
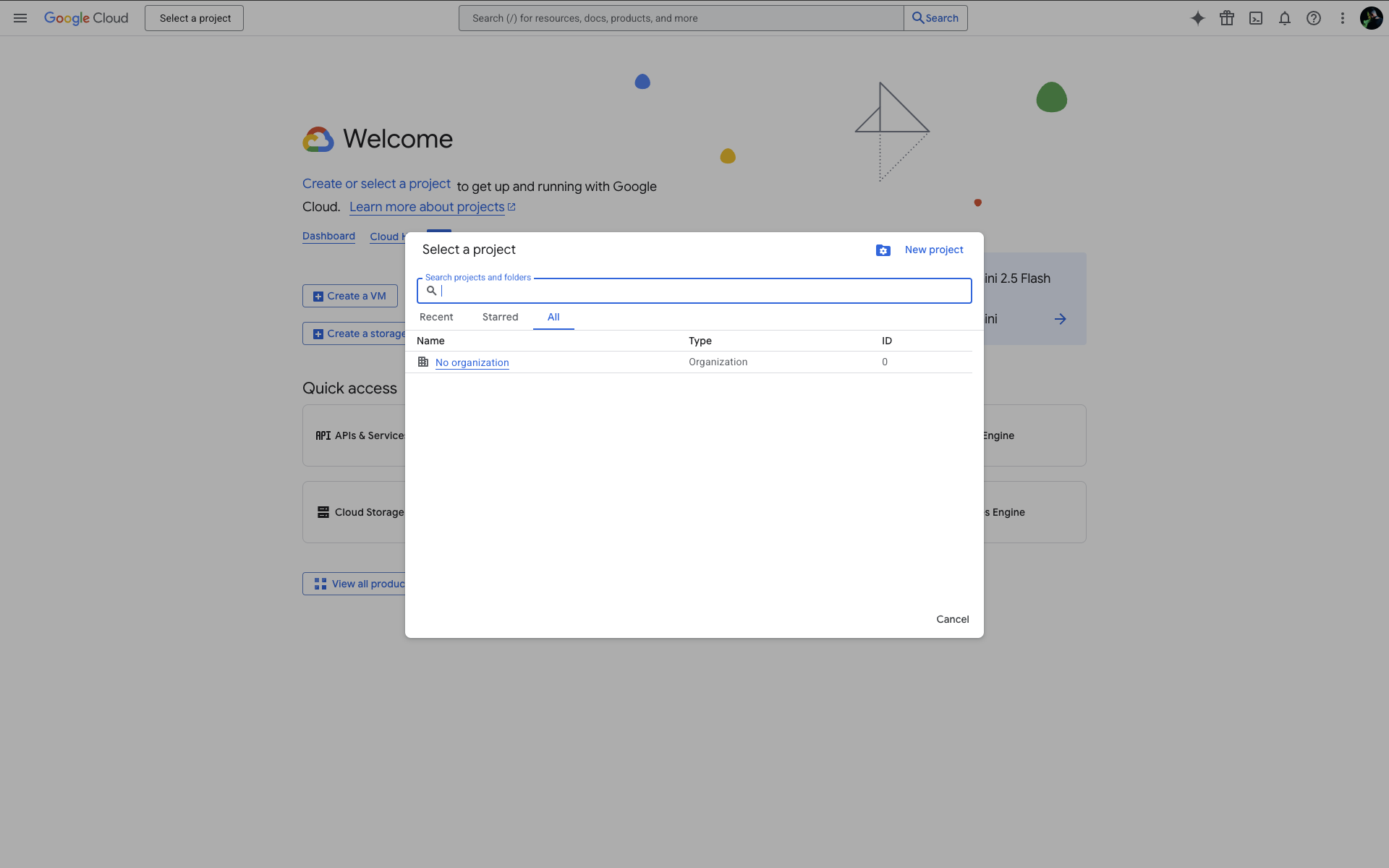
- Enable the project: Ensure the project is active and selected
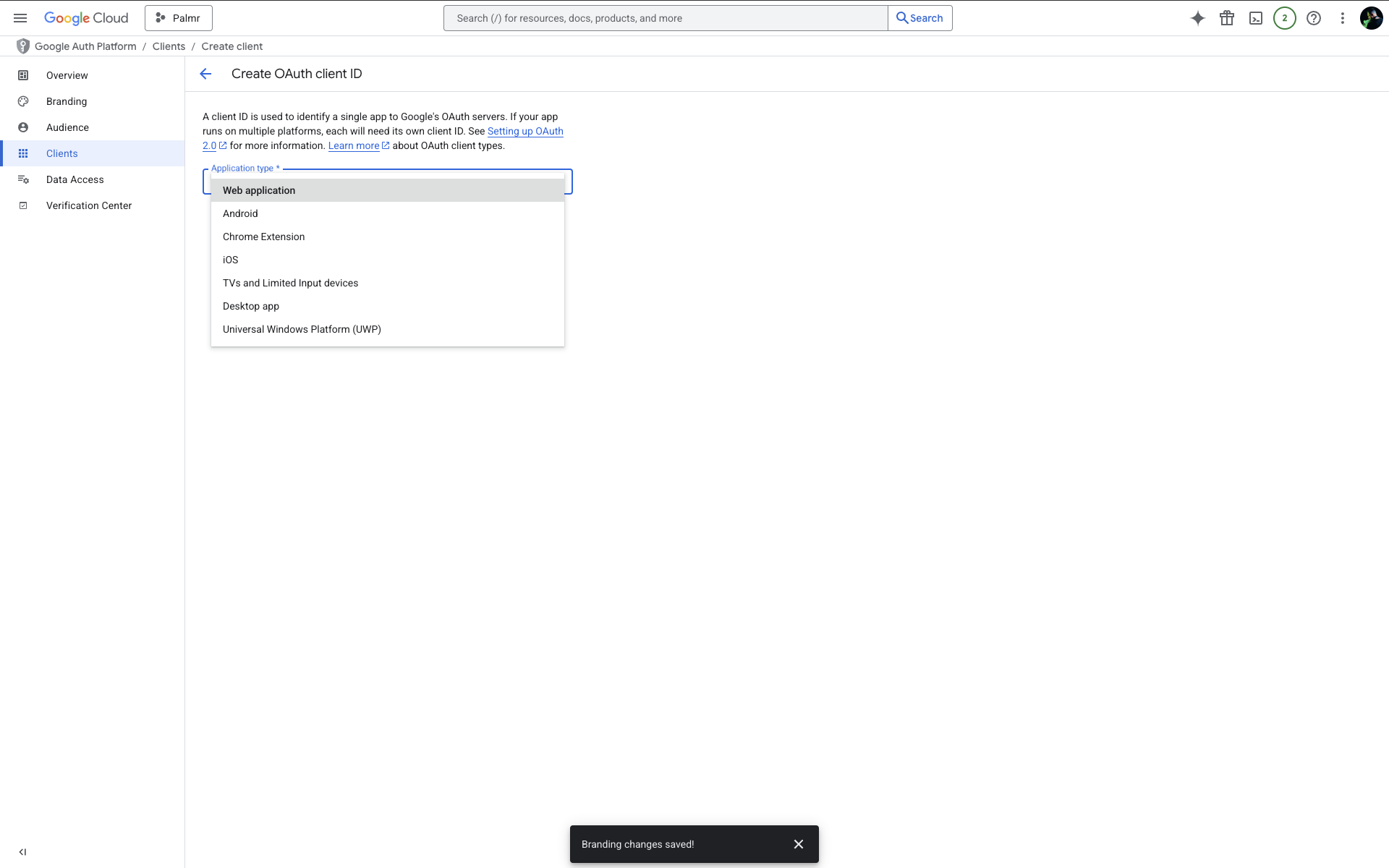
Configuring OAuth consent screen
The OAuth consent screen is what users see when they authenticate with Google.
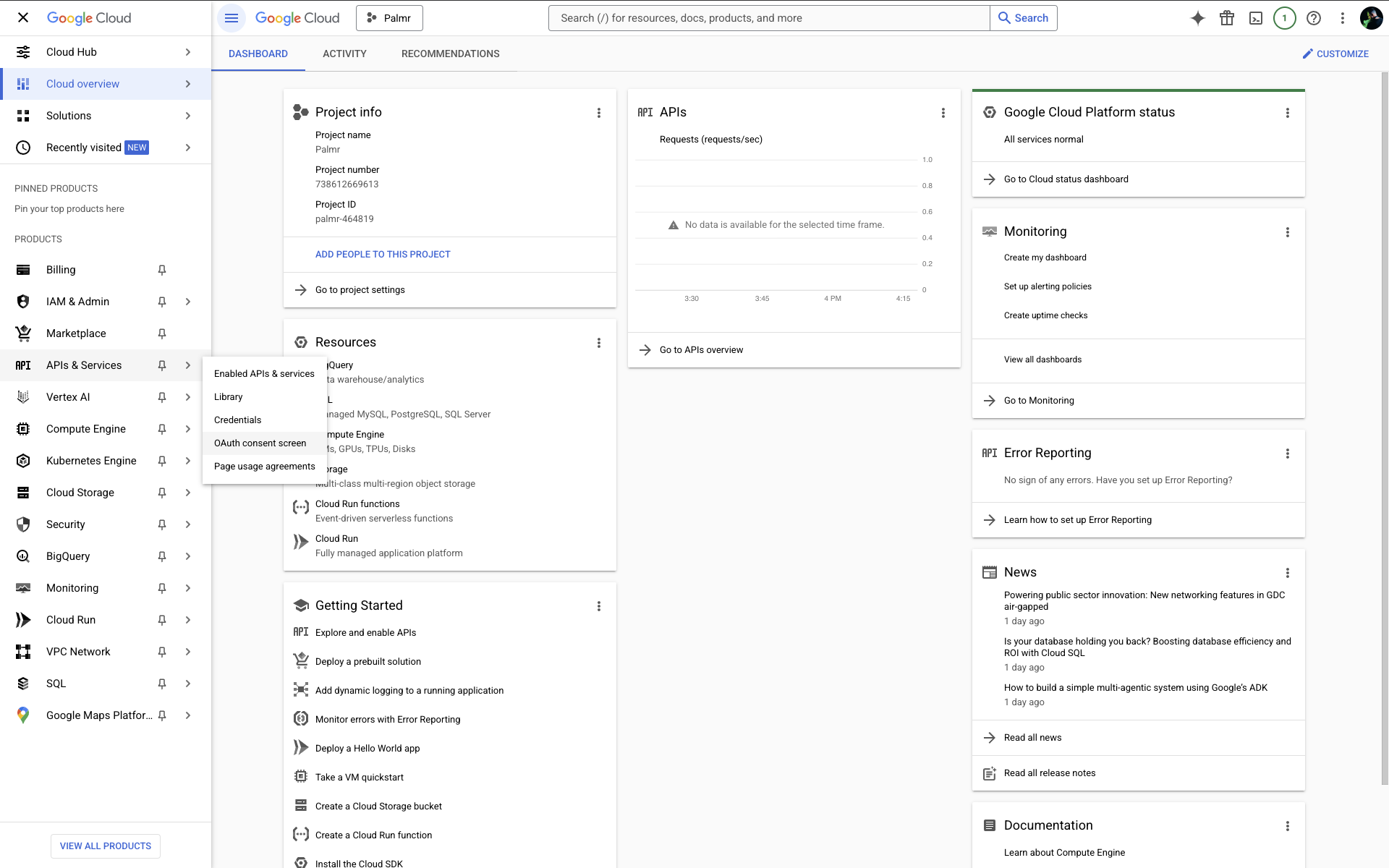
- Access OAuth consent screen: Navigate to APIs & Services > OAuth consent screen
- Choose user type:
- Internal - For Google Workspace organizations (users within your domain only)
- External - For public use (any Google user can authenticate)
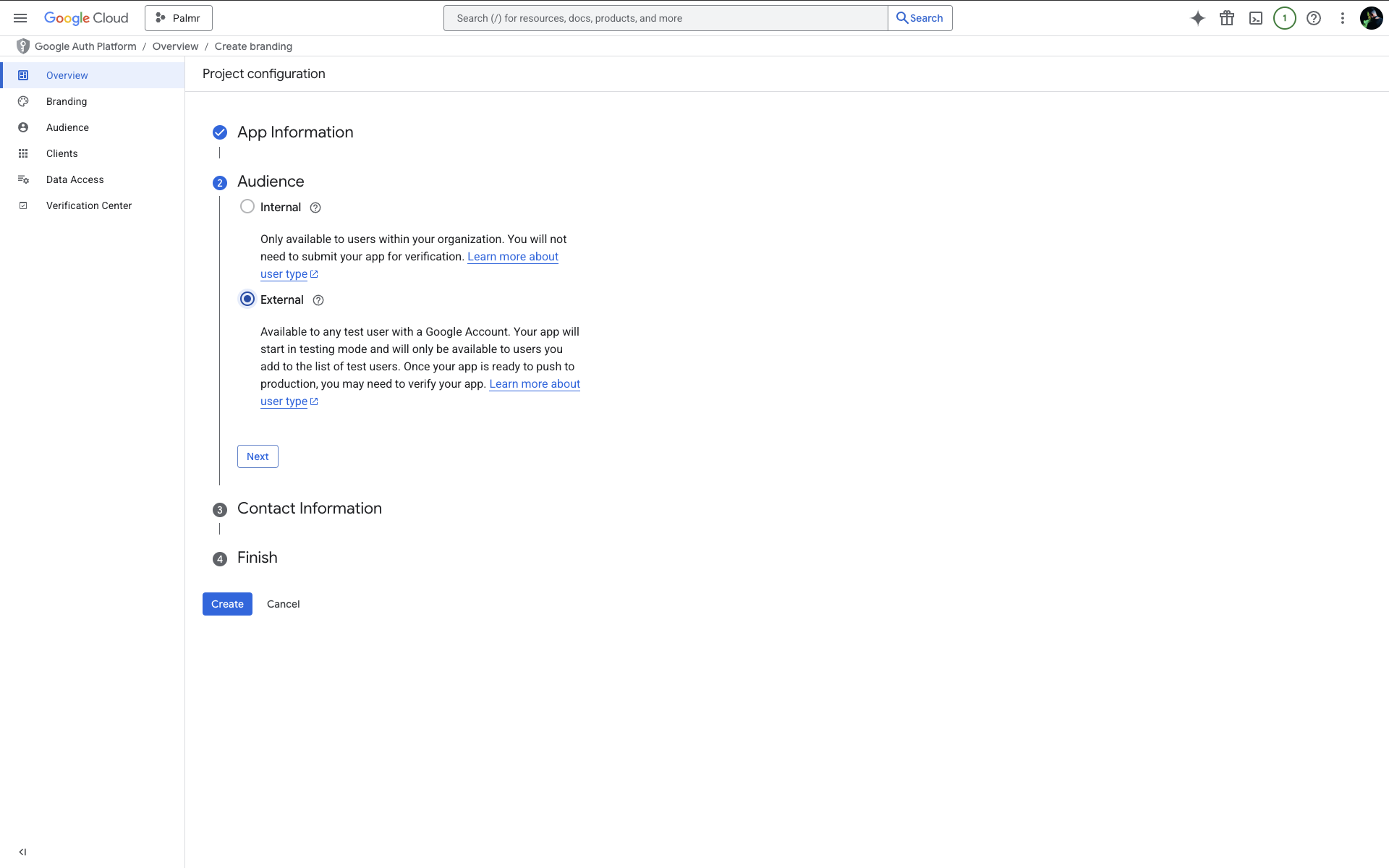
- Fill required information:
- Application name: Enter a descriptive name like "Palmr File Sharing"
- User support email: Provide a valid support email address
- Developer contact information: Add your contact email for Google communications
Tip: For business use, choose "Internal" if you have Google Workspace. This restricts access to your organization's users and simplifies the approval process.
Creating OAuth 2.0 credentials
Now you'll create the actual credentials that Palmr will use to authenticate with Google.
- Navigate to Credentials: Go to APIs & Services > Credentials
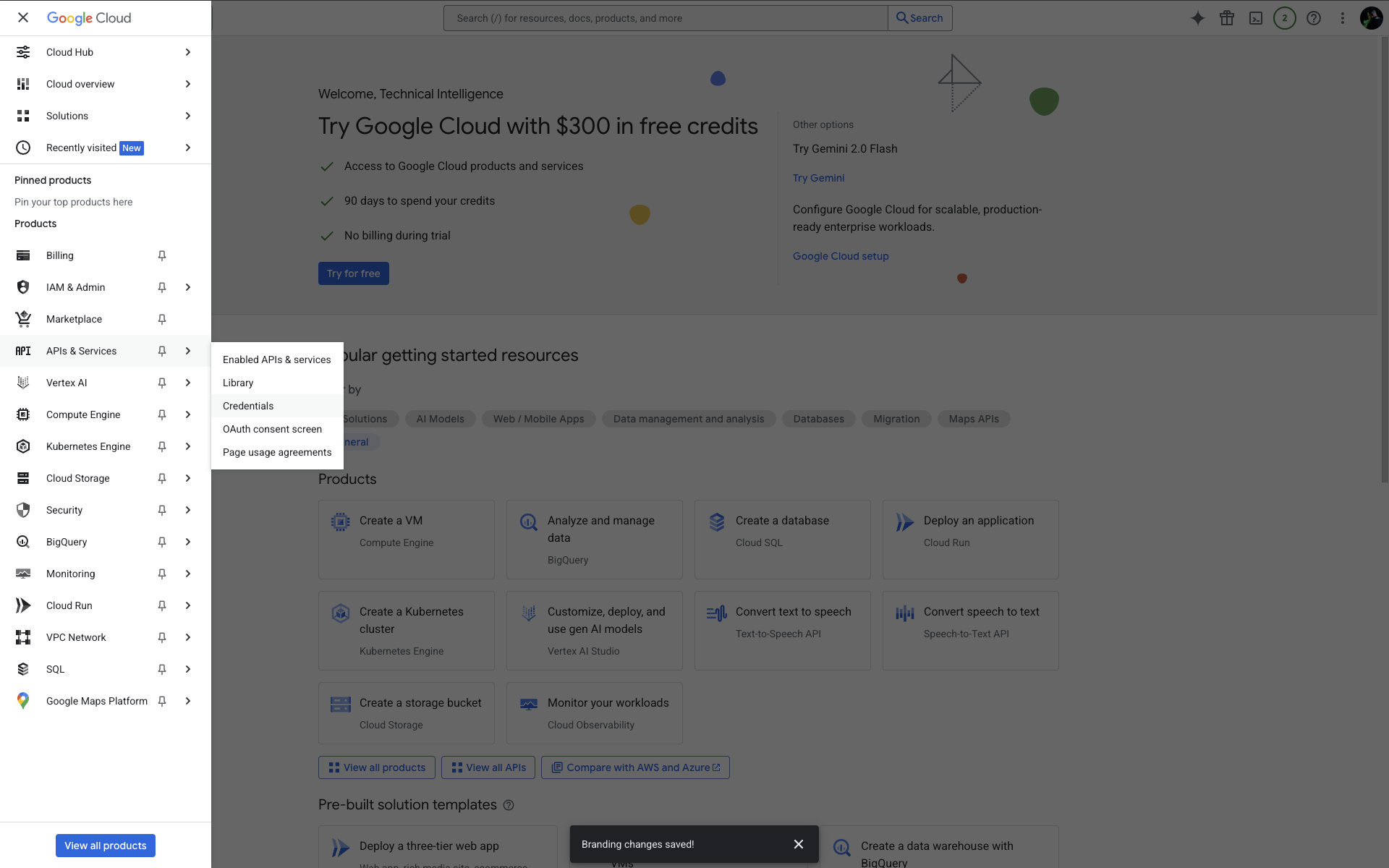
- Create OAuth client: Click + CREATE CREDENTIALS > OAuth client ID
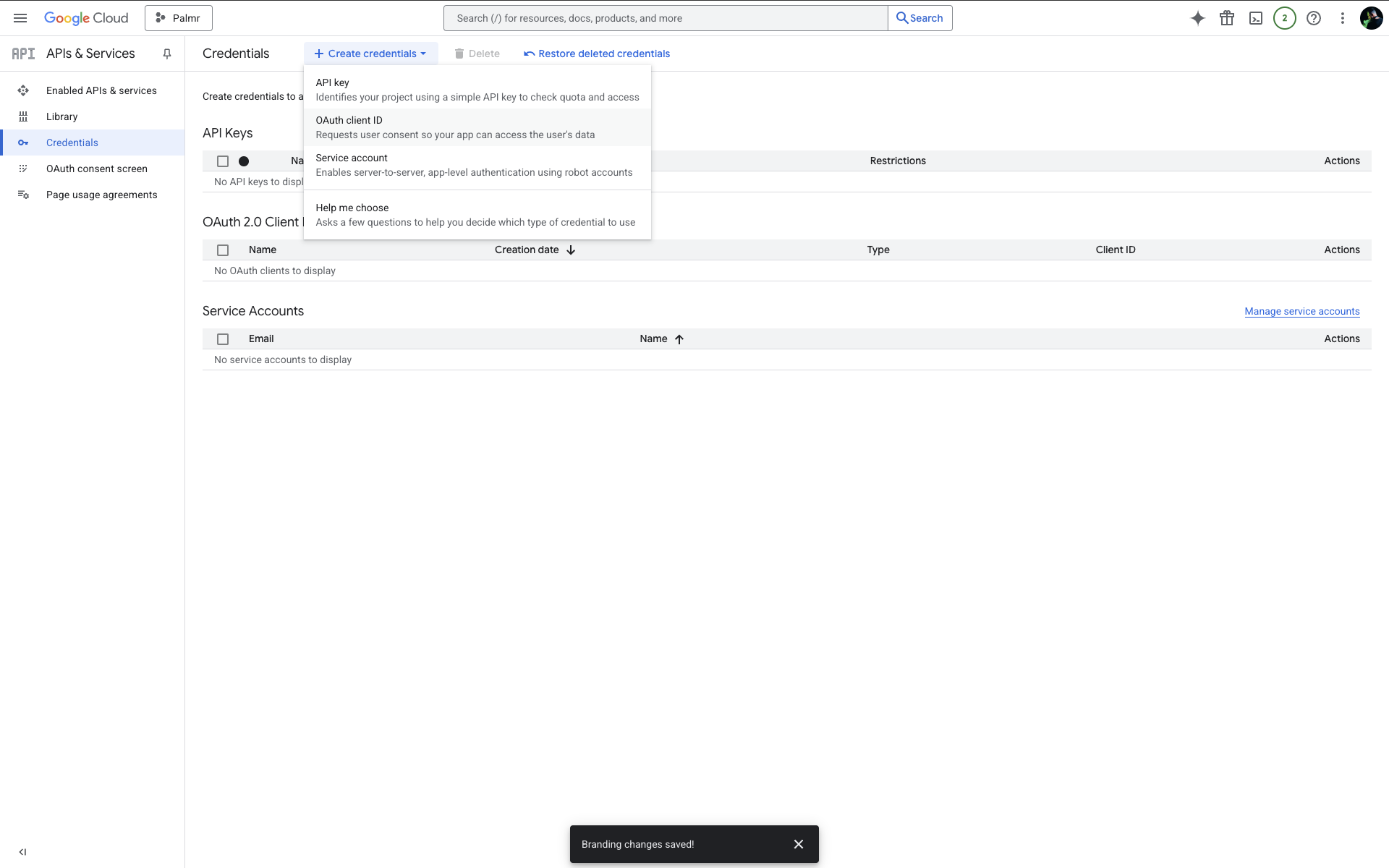
- Select application type: Choose Web application
- Configure authorized URIs and authorized redirect URIs:
You'll need to configure several URLs in your Google Cloud Console credentials. Here's what to add for each environment:
Authorized URIs
| Environment | URL |
|---|---|
| Production | https://yourdomain.com |
| Development | http://localhost:3000 |
| Custom Port | https://yourdomain.com:5487 |
Authorized Redirect URIs
| Environment | URL |
|---|---|
| Production | https://yourdomain.com/api/auth/providers/google/callback |
| Development | http://localhost:3000/api/auth/providers/google/callback |
| Custom Port | https://yourdomain.com:5487/api/auth/providers/google/callback |
Note: Replace
yourdomain.comwith your actual domain name in all production and custom port URLs. Note: You can add multiple redirect URIs for different environments (development, staging, production).
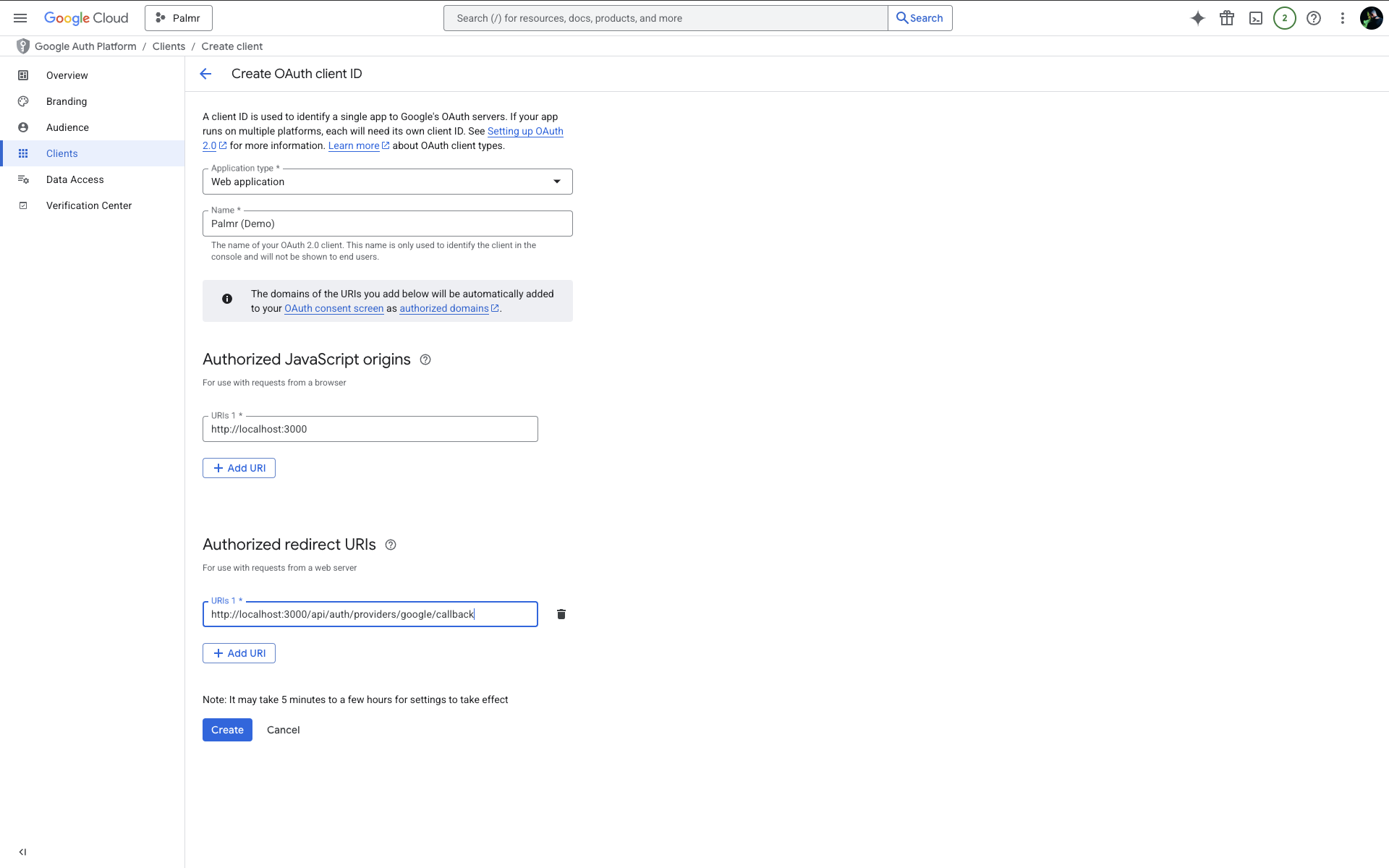
- Create and save credentials: Click Create and copy both the Client ID and Client Secret
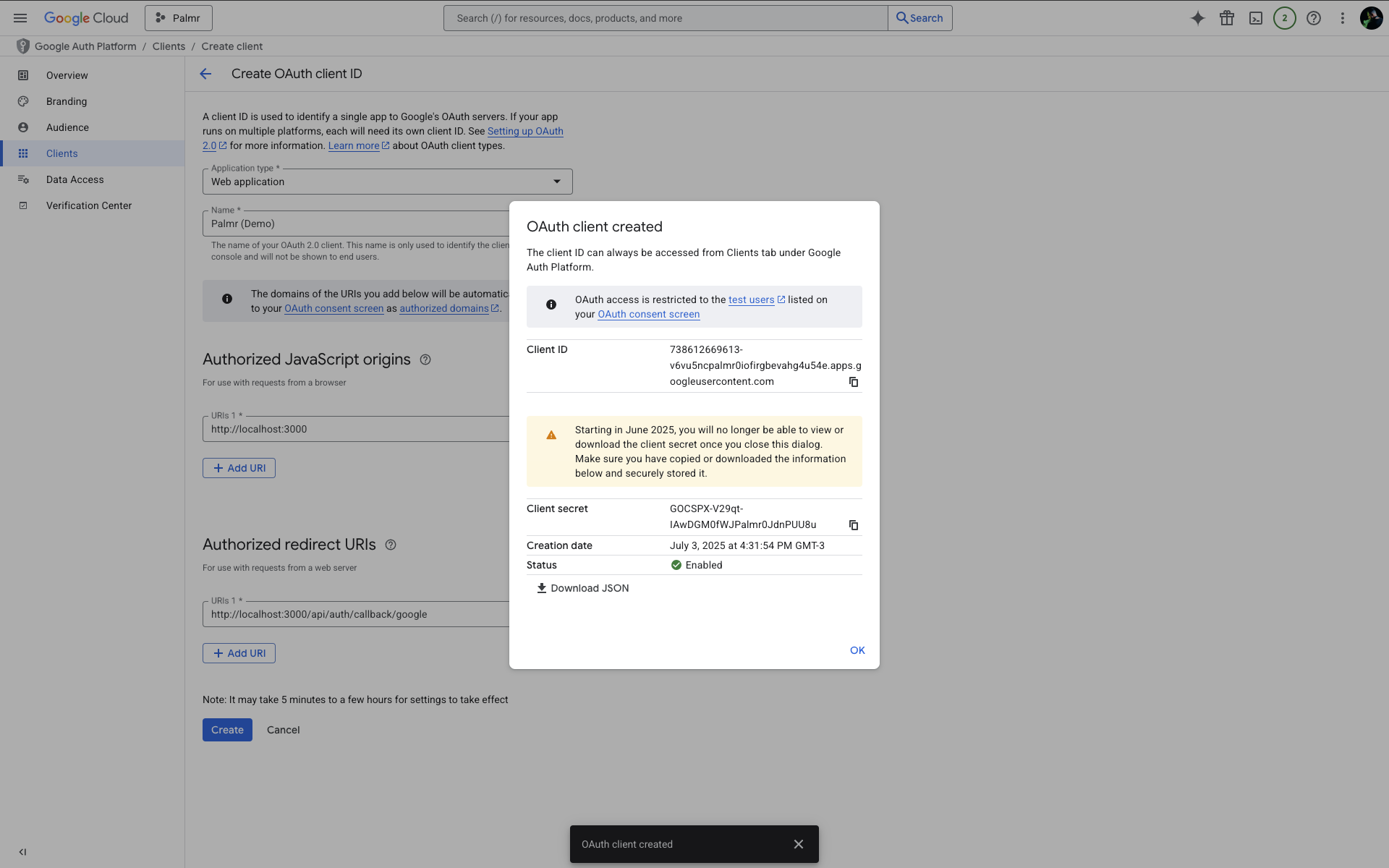
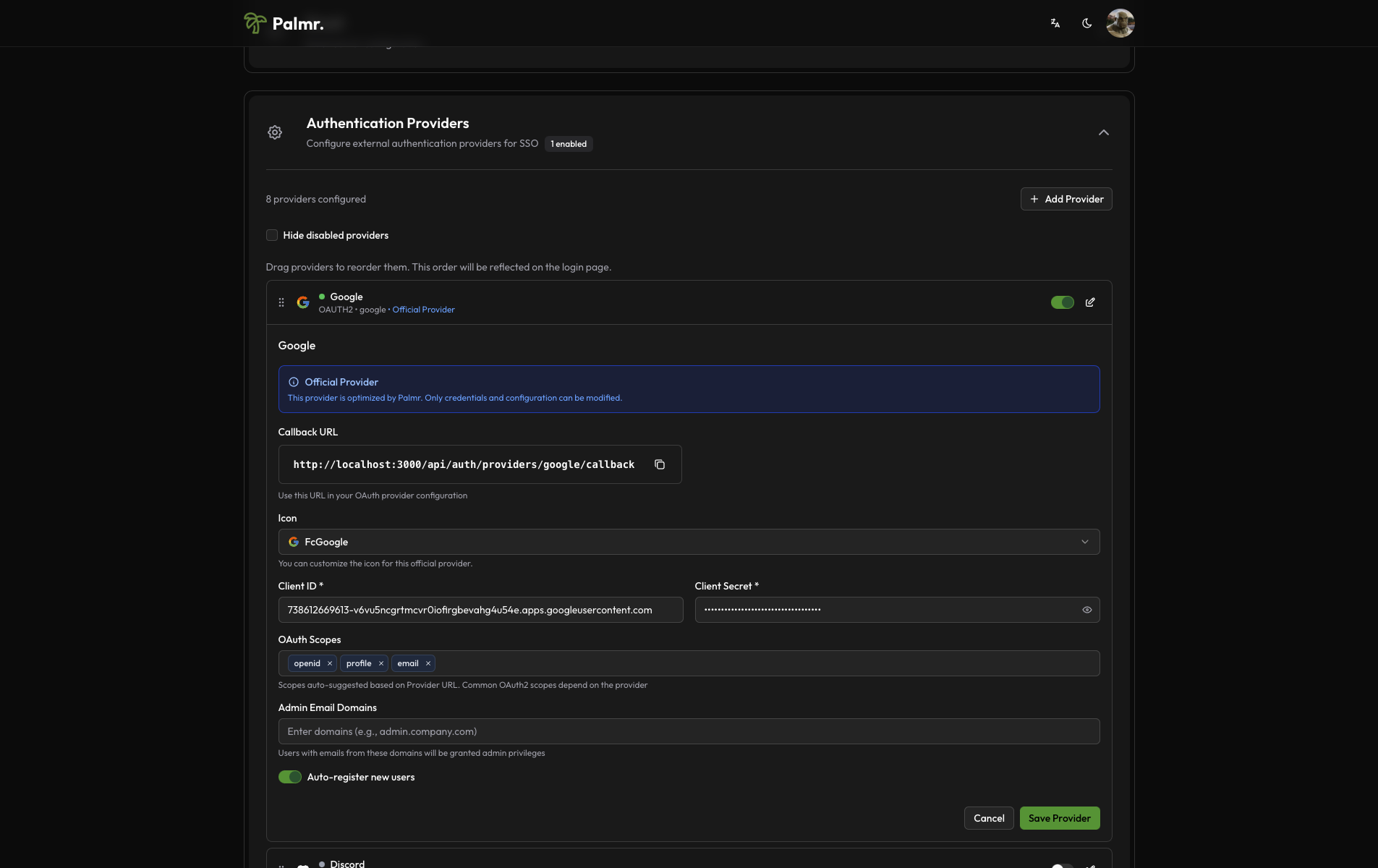
The client ID and client secret shown in the image are examples only (fake credentials). You must use your own credentials from Google Cloud Console.
Important: Replace
yourdomain.comwith your actual domain. You can add multiple URIs for different environments (development, staging, production).
Configuring Palmr
Accessing OIDC settings
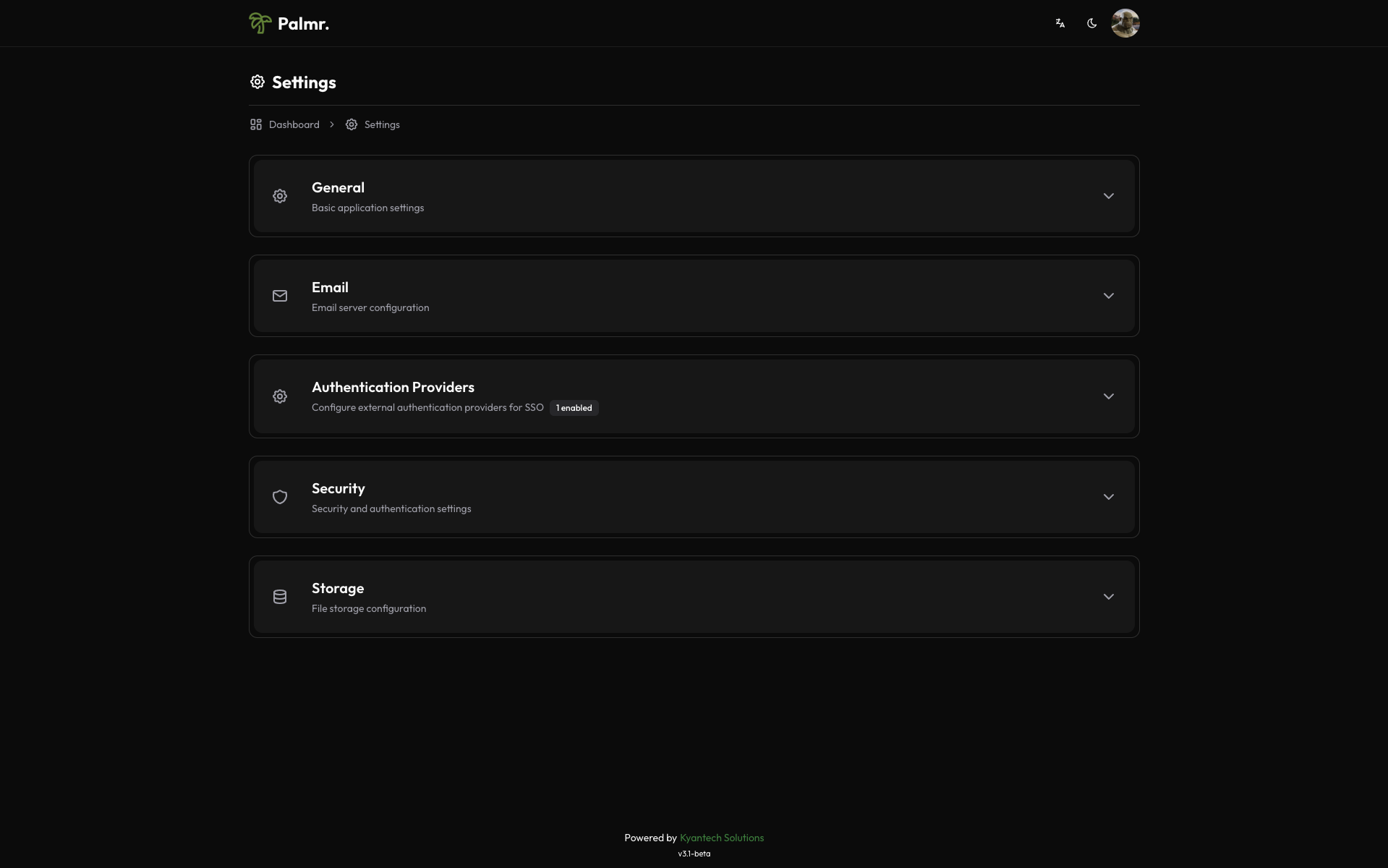
To configure Google authentication in Palmr, you need administrator access to the settings panel.
-
Login as administrator: Sign in to Palmr with an admin account
-
Access settings: Click your profile picture in the header and select Settings
-
Navigate to authentication: Find and click on the Authentication Providers configuration section
Enabling Google provider
Google comes pre-configured as an official provider, so the setup process is streamlined.
-
Locate Google provider: Find Google in the list of available providers
-
Enable the provider: Toggle the status to Enabled
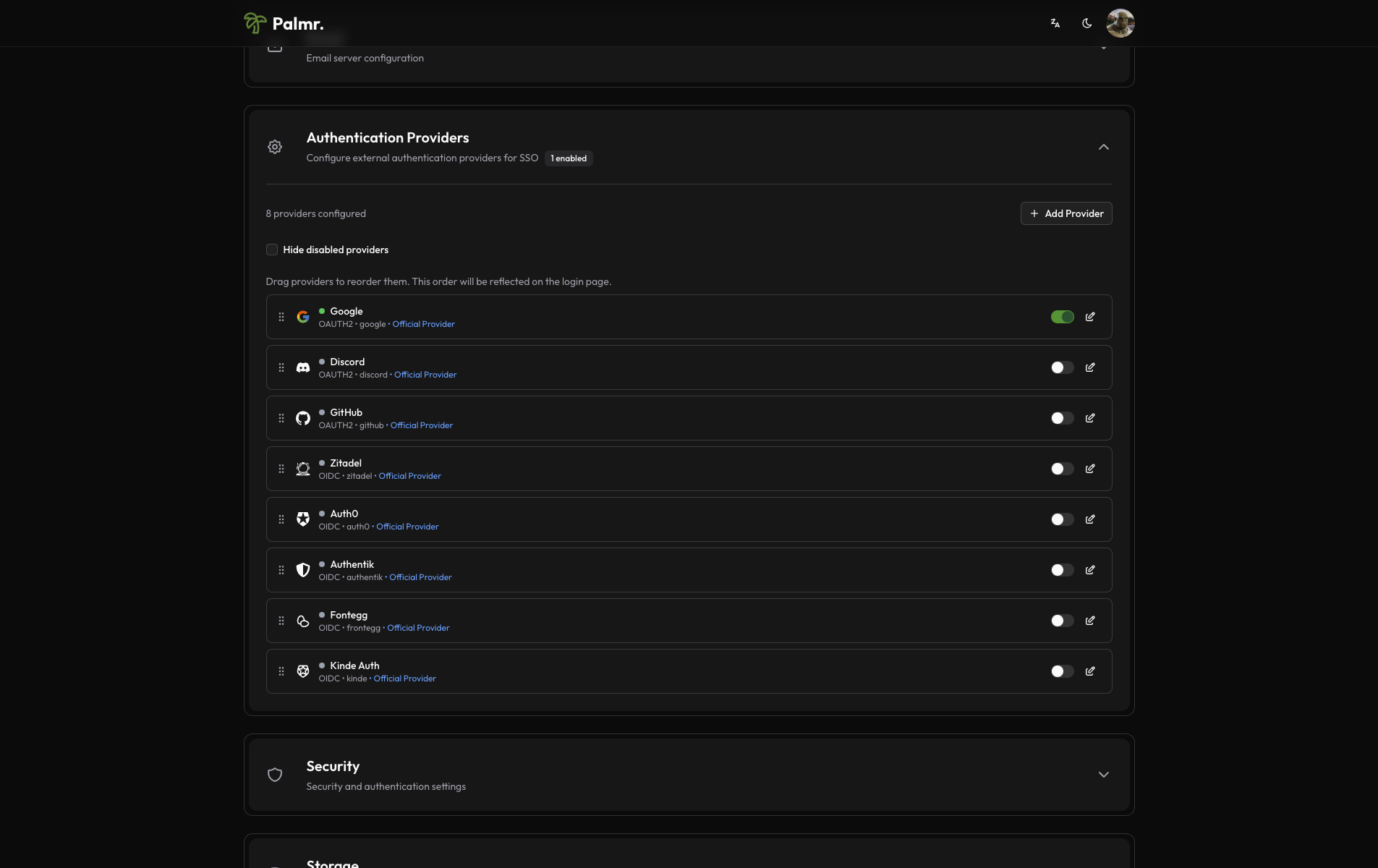
After enabling the provider, click on the pen icon to configure the provider.
- Configure credentials:
- Client ID: Paste the Client ID from Google Cloud Console
- Client Secret: Paste the Client Secret from Google Cloud Console
- Scopes: Add the scopes you want to use. The default scopes are
openid,profile, andemail.
Advanced configuration options
Configure additional settings to customize the authentication behavior:
Auto Registration: Enable this to automatically create user accounts when someone authenticates for the first time.
Admin Email Domains: Specify domains that should automatically receive admin privileges. For example, entering yourcompany.com will grant admin access to anyone with an email from that domain.
Sort Order: Control where the Google login button appears relative to other authentication providers.
Icon: you can choose the icon you want to use for the Google login button (default is FcGoogle).
Security consideration: Be cautious with auto-registration and admin domains. Only enable these if you trust the user base or have domain restrictions in place.
Account linking
By default, if a user is already registered in Palmr with their Google email, they will be automatically linked to their Palmr account.
Note: You can't disable account linking. If you want to unlink a user from their Google account, you need to delete the user from Palmr.
Technical configuration
Google's technical configuration is handled automatically, but understanding the setup can help with troubleshooting:
Field mappings
Palmr automatically maps Google user information to local user accounts:
- User ID: Maps from Google's
subfield - Email: Maps from Google's
emailfield - Full Name: Maps from Google's
namefield - First Name: Maps from Google's
given_namefield - Last Name: Maps from Google's
family_namefield - Avatar: Maps from Google's
picturefield
Testing the configuration
Verifying the setup
After configuring Google authentication, test the integration to ensure everything works correctly.
-
Check login page: Navigate to your Palmr login page and verify the "Sign in with Google" button appears
-
Test authentication flow: Click the Google sign-in button and complete the authentication process
-
Verify user creation: Confirm that a new user account is created (if auto-registration is enabled)
Login flow verification
The complete authentication process should work as follows:
- User clicks "Sign in with Google": The browser redirects to Google's authentication page
- User authenticates with Google: User enters their Google credentials or confirms existing session
- Google redirects back to Palmr: User returns to Palmr with authentication tokens
- Palmr creates or updates user: User account is automatically managed based on your configuration
- User accesses Palmr: User is logged in and can use all features according to their permissions
Troubleshooting common issues
Redirect URI mismatch error
Error message: Error 400: redirect_uri_mismatch
Cause: The redirect URI in your request doesn't match what's configured in Google Cloud Console.
Solution:
- Check the exact URL in the error message
- Add this exact URL to your Google Cloud Console credentials
- Ensure you include the correct protocol (http/https) and port
- Remove any trailing slashes unless they're in the error message
Access denied error
Error message: Error 403: access_denied
Cause: User denied permissions or the OAuth consent screen isn't properly configured.
Solution:
- Verify the OAuth consent screen is published (for External user type)
- Check that required scopes are correctly configured
- For Internal applications, ensure the user belongs to your Google Workspace organization
- Review and simplify the permissions you're requesting
Invalid client error
Error message: Error 401: invalid_client
Cause: Incorrect Client ID or Client Secret.
Solution:
- Double-check that you've copied the credentials correctly from Google Cloud Console
- Ensure there are no extra spaces or characters in the credentials
- Regenerate credentials if necessary
- Verify you're using the correct project in Google Cloud Console
Discovery endpoint issues
Cause: Network connectivity problems or DNS resolution issues.
Solution:
- Check server firewall and network connectivity
- Verify DNS resolution from your server
- Consider proxy or CDN configurations that might block the request
Security best practices
Credential management
- Never expose secrets: Keep your Client Secret secure and never commit it to version control
- Rotate credentials regularly: Generate new credentials periodically for enhanced security
- Use environment variables: Store sensitive configuration in environment variables, not config files
- Monitor access logs: Regularly review authentication logs for suspicious activity
Domain and user restrictions
- Limit admin domains: Only add trusted domains to the admin list
- Review auto-registration: Consider disabling auto-registration if you need manual user approval
- Use Internal OAuth: For organizations with Google Workspace, use Internal OAuth consent screen
- Regular access reviews: Periodically review user access and remove inactive accounts
Production considerations
- Use HTTPS: Always use HTTPS in production environments
- Configure proper domains: Use production domains in Google Cloud Console
- Test thoroughly: Verify the complete authentication flow before going live
- Plan for failures: Have fallback authentication methods available
Next steps
With Google authentication configured, you might want to:
- Configure additional providers: Set up other OIDC providers for more authentication options
- Customize user management: Fine-tune auto-registration and admin assignment rules
- Review security settings: Ensure your authentication setup meets your security requirements
- Monitor usage: Keep track of authentication patterns and user activity
For more information about OIDC authentication in Palmr, see the OIDC Authentication overview.