Frontegg
Frontegg is one of Palmr's officially supported OIDC providers, offering enterprise-grade authentication through Frontegg's identity platform. This integration allows users to sign in to Palmr using Frontegg's comprehensive authentication system, making it perfect for enterprise organizations, applications requiring advanced security features, and teams that need centralized identity management with modern developer experience.
Why use Frontegg authentication?
Frontegg authentication provides several advantages for enterprise and developer-focused organizations:
- Modern developer experience - Clean APIs, comprehensive SDKs, and developer-friendly tools
- Enterprise-grade security - Advanced security features like MFA, adaptive authentication, and threat detection
- Centralized identity management - Single platform to manage users across multiple applications
- Compliance ready - Built-in compliance with GDPR, SOC 2, and other enterprise standards
- Advanced customization - Themes, flows, and custom branding capabilities
Prerequisites
Before configuring Frontegg authentication, ensure you have:
- Frontegg account - Ability to create applications and manage tenants
- Admin privileges in Palmr - Required to configure OIDC settings
- Domain configuration - For production deployments with custom domains
Note: Frontegg is pre-configured as an official provider in Palmr, which means the technical configuration is handled automatically. You only need to provide your OAuth credentials.
Setting up Frontegg Application
Creating a Frontegg application
To get started with Frontegg authentication, you'll need to create an application in your Frontegg Admin Portal.
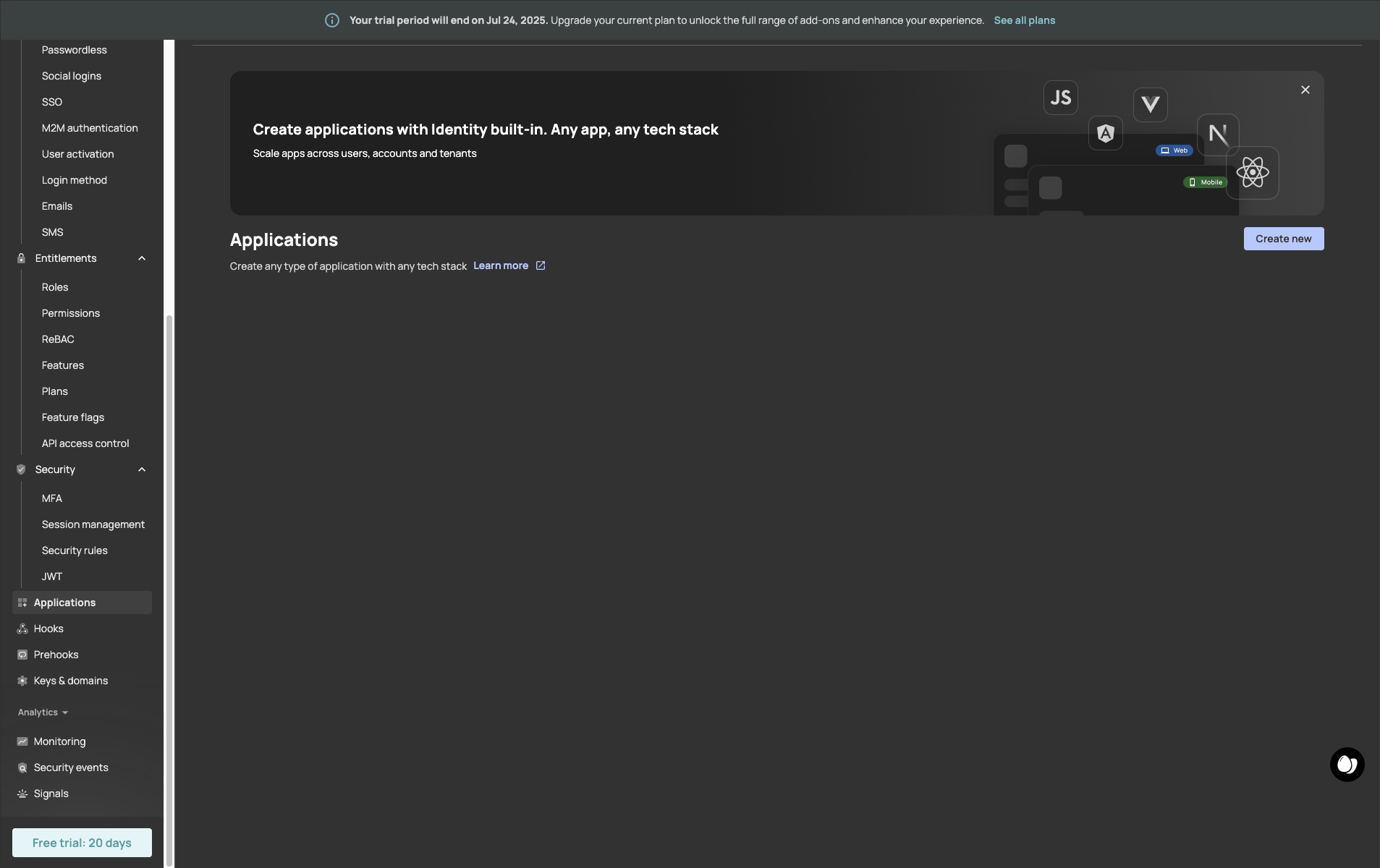
- Navigate to Frontegg Admin Portal: Go to https://portal.frontegg.com/development/applications for example. (Development environment) for production environment you need to go to https://portal.frontegg.com/production/applications - This can change depending on your environment.
-
Create new application: Click "Create new"
-
Fill application details:
- Name: Enter a descriptive name like "Palmr File Sharing"
- Description: Add a clear description of your Palmr instance
- Type: Choose "Web" for web-based Palmr instances
- Frontend stack: Choose "React" for web-based Palmr instances
- App URL: Add the URL of your Palmr instance, see table below for the example of the URL.
Environment URL Production https://yourdomain.com/api/auth/providers/frontegg/callbackDevelopment http://localhost:3000/api/auth/providers/frontegg/callbackCustom Port https://yourdomain.com:5487/api/auth/providers/frontegg/callbackNote: Replace
yourdomain.comwith your actual domain name in all production and custom port URLs.
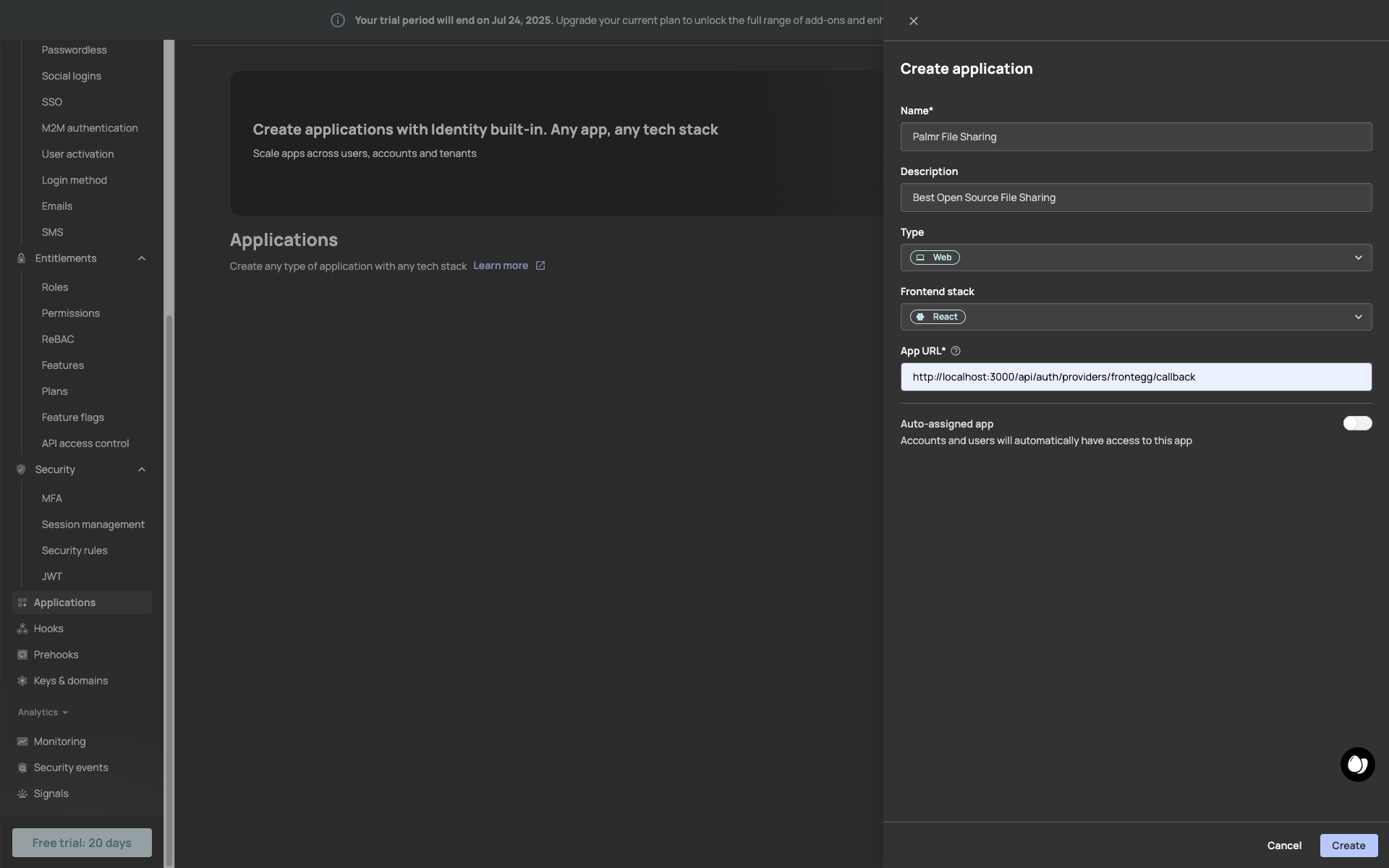
This is a fake application, you have to use your own.
- Create application: Click "Create" to generate your Frontegg application
Configuring application settings
After creating your application, you'll need to get the settings that Palmr will use. You gonna be redirected to the application page, where you can see the application details.
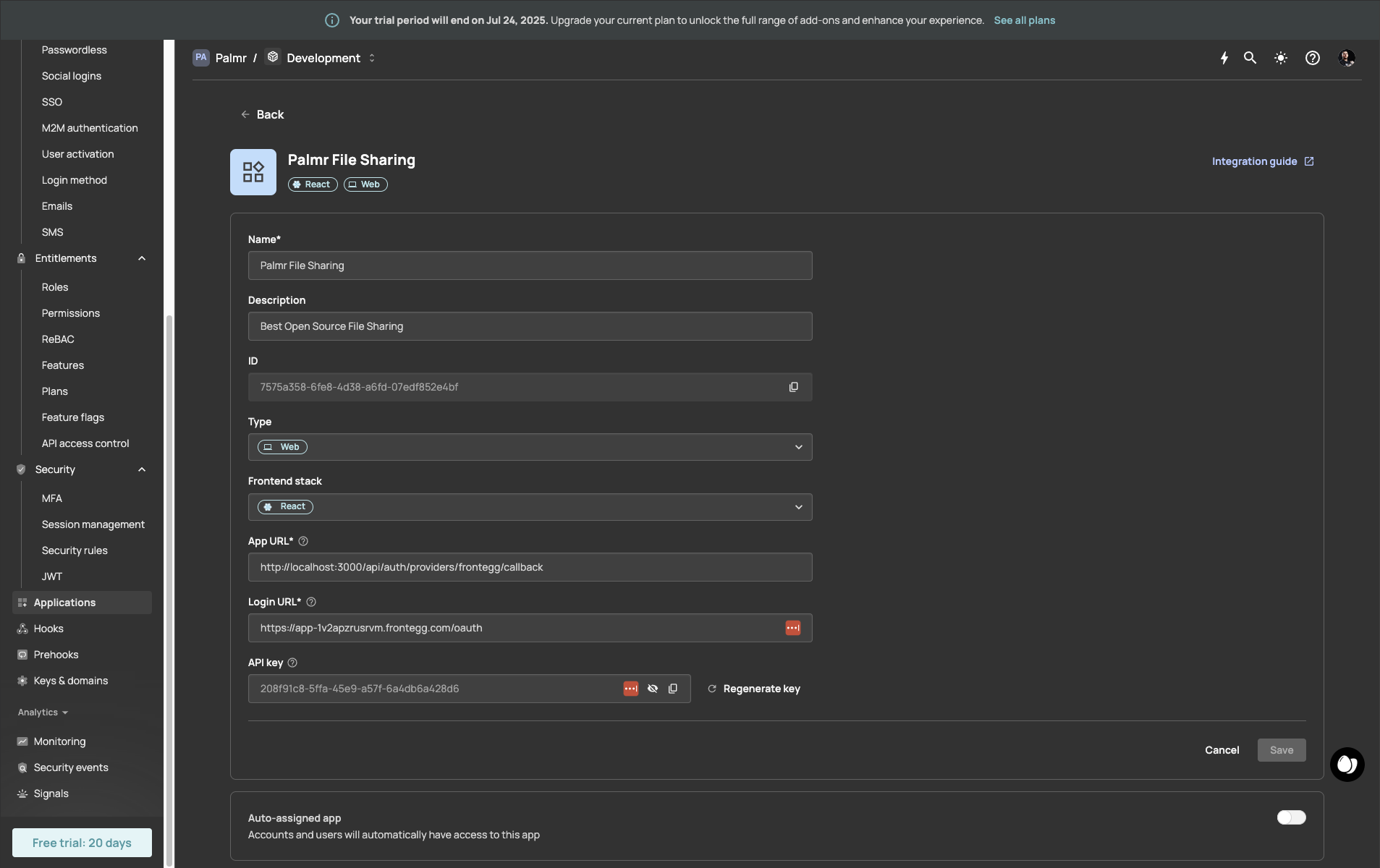
This is a fake application, you have to use your own.
Getting OAuth credentials
Now you'll get the credentials that Palmr will use to authenticate with Frontegg.
-
Copy Domain: Note your Frontegg domain (e.g.,
your-tenant.frontegg.com) - You can find it in the application page at field "Login URL". But copy just the domain, without the path. -
Copy Client ID: You can find it in the application page at field "ID" in the application page.
-
Copy Client Secret: You can find it in the application page at field "API key" in the application page.
In Frontegg we finished the configuration, but we need to configure Palmr to use it.
Configuring Palmr
Accessing OIDC settings
To configure Frontegg authentication in Palmr, you need administrator access to the settings panel.
-
Login as administrator: Sign in to Palmr with an admin account
-
Access settings: Click your profile picture in the header and select Settings
-
Navigate to authentication: Find and click on the Authentication Providers configuration section
Enabling Frontegg provider
Frontegg comes pre-configured as an official provider, so the setup process is streamlined.
-
Locate Frontegg provider: Find Frontegg in the list of available providers
-
Enable the provider: Toggle the status to Enabled
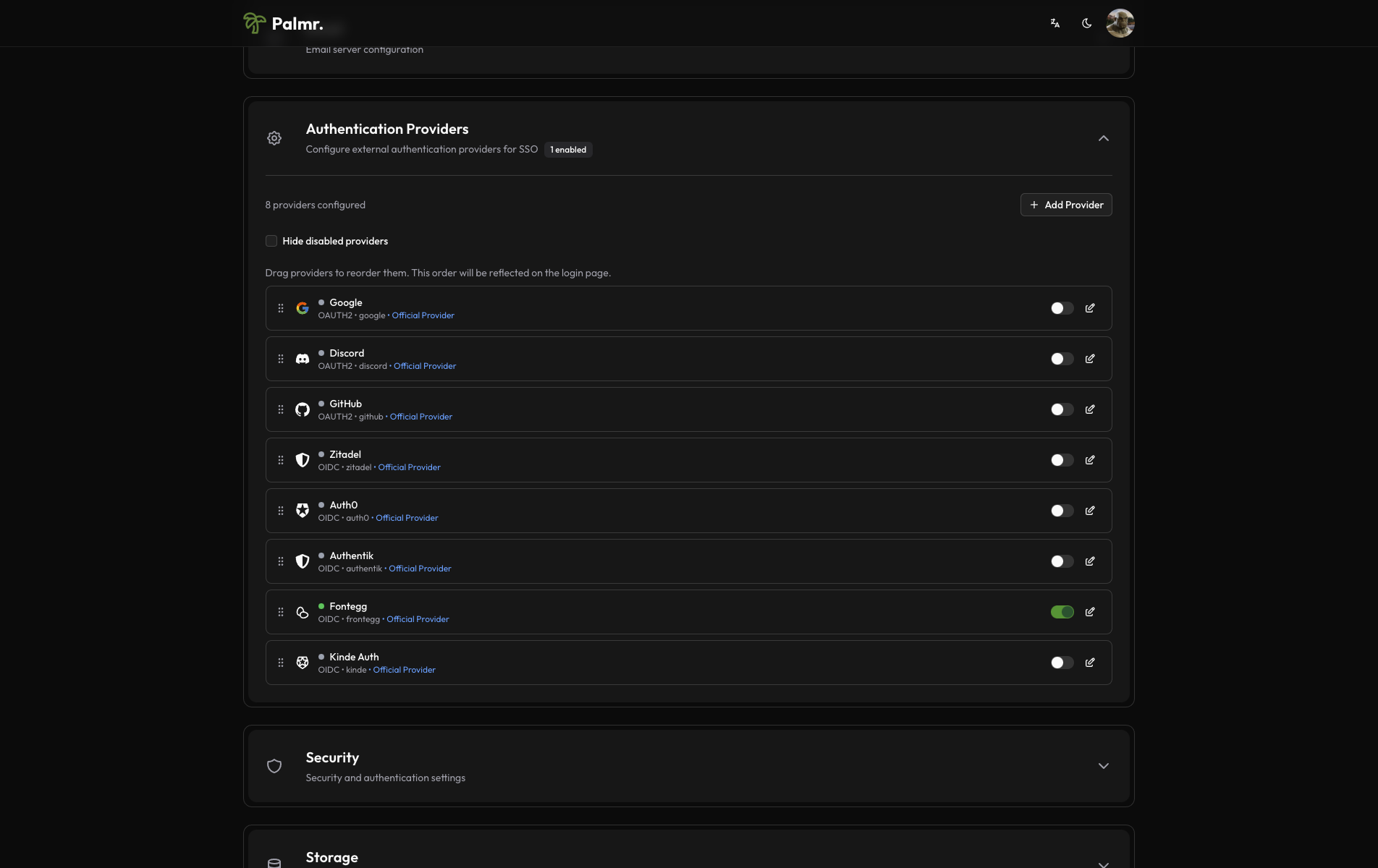
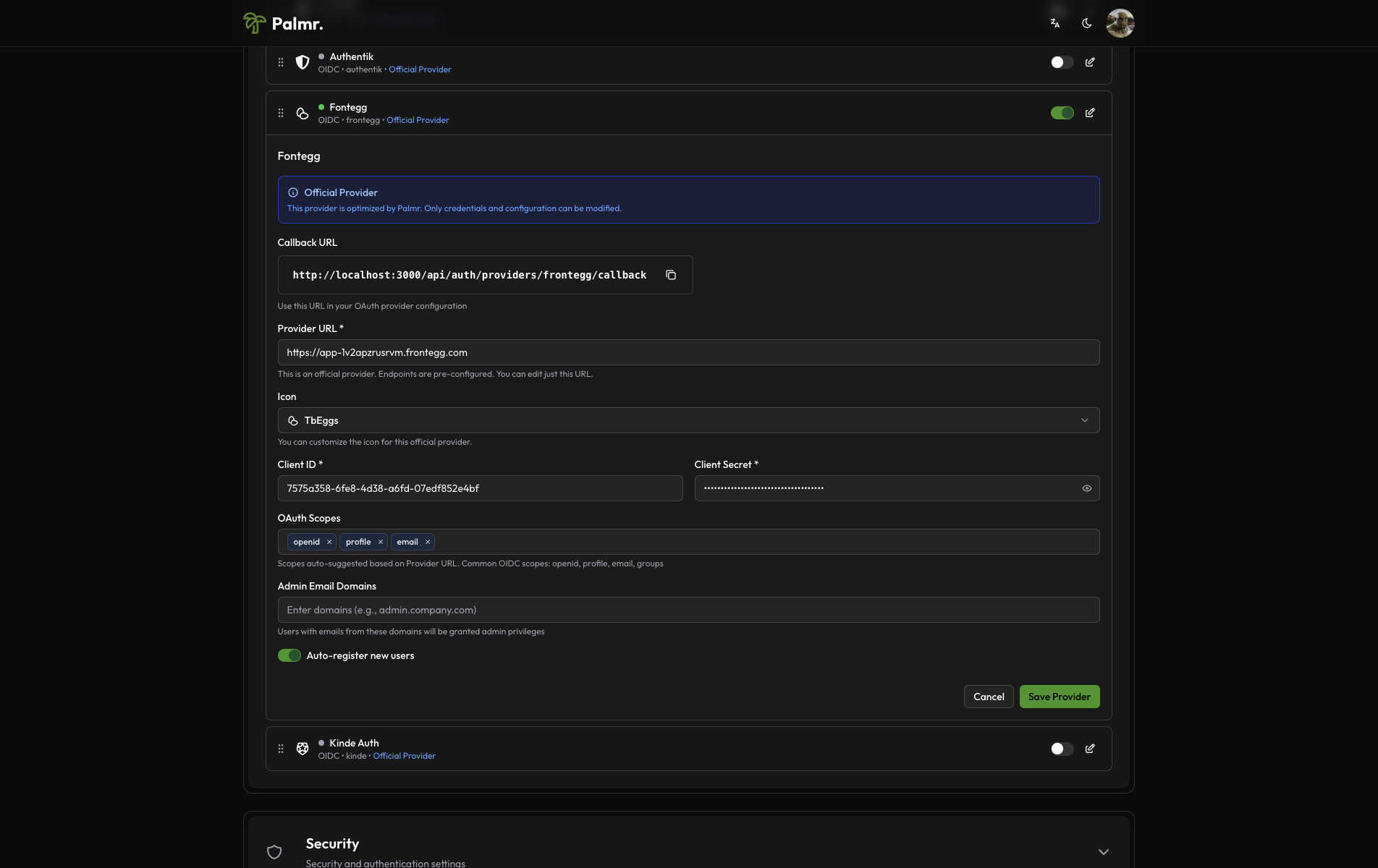
After enabling the provider, click on the pen icon to configure the provider.
- Configure credentials:
- Provider URL: Paste your Frontegg domain (e.g.,
https://your-tenant.frontegg.com) - It's the same "Login URL" you copied in the previous step. - Client ID: Paste the Client ID from Frontegg application - It's the same "ID" you copied in the previous step.
- Client Secret: Paste the Client Secret from Frontegg application - It's the same "API key" you copied in the previous step.
- Scopes: Add the scopes you want to use. The default scopes are
openid,profile, andemail. You don't need to change this, but you can if you want.
- Provider URL: Paste your Frontegg domain (e.g.,
This is a fake application, you have to use your own.
Advanced configuration options
Configure additional settings to customize the authentication behavior:
Auto Registration: Enable this to automatically create user accounts when someone authenticates for the first time.
Sort Order: Control where the Frontegg login button appears relative to other authentication providers.
Icon: you can choose the icon you want to use for the Frontegg login button (default is TbEggs).
Developer tip: Frontegg authentication works great for organizations requiring modern developer experience and enterprise-grade security features.
Account linking
By default, if a user is already registered in Palmr with their Frontegg email, they will be automatically linked to their Palmr account.
Note: You can't disable account linking. If you want to unlink a user from their Frontegg account, you need to delete the user from Palmr.
Technical configuration
Frontegg's technical configuration is handled automatically, but understanding the setup can help with troubleshooting:
Field mappings
Palmr automatically maps Frontegg user information to local user accounts:
- User ID: Maps from Frontegg's
subfield - Email: Maps from Frontegg's
emailfield - Full Name: Maps from Frontegg's
namefield - First Name: Maps from Frontegg's
given_namefield - Last Name: Maps from Frontegg's
family_namefield - Avatar: Maps from Frontegg's
picturefield - Username: Maps from Frontegg's
preferred_usernamefield
Frontegg-specific features
- Custom Claims: Can include custom user metadata and app metadata
- Themes Support: Can customize authentication UI with custom themes
- Multi-factor Authentication: Supports Frontegg's MFA features
- Enterprise SSO: Integrates with SAML, LDAP, and other enterprise systems
- Modern APIs: Clean REST APIs and comprehensive SDKs
Testing the configuration
Verifying the setup
After configuring Frontegg authentication, test the integration to ensure everything works correctly.
-
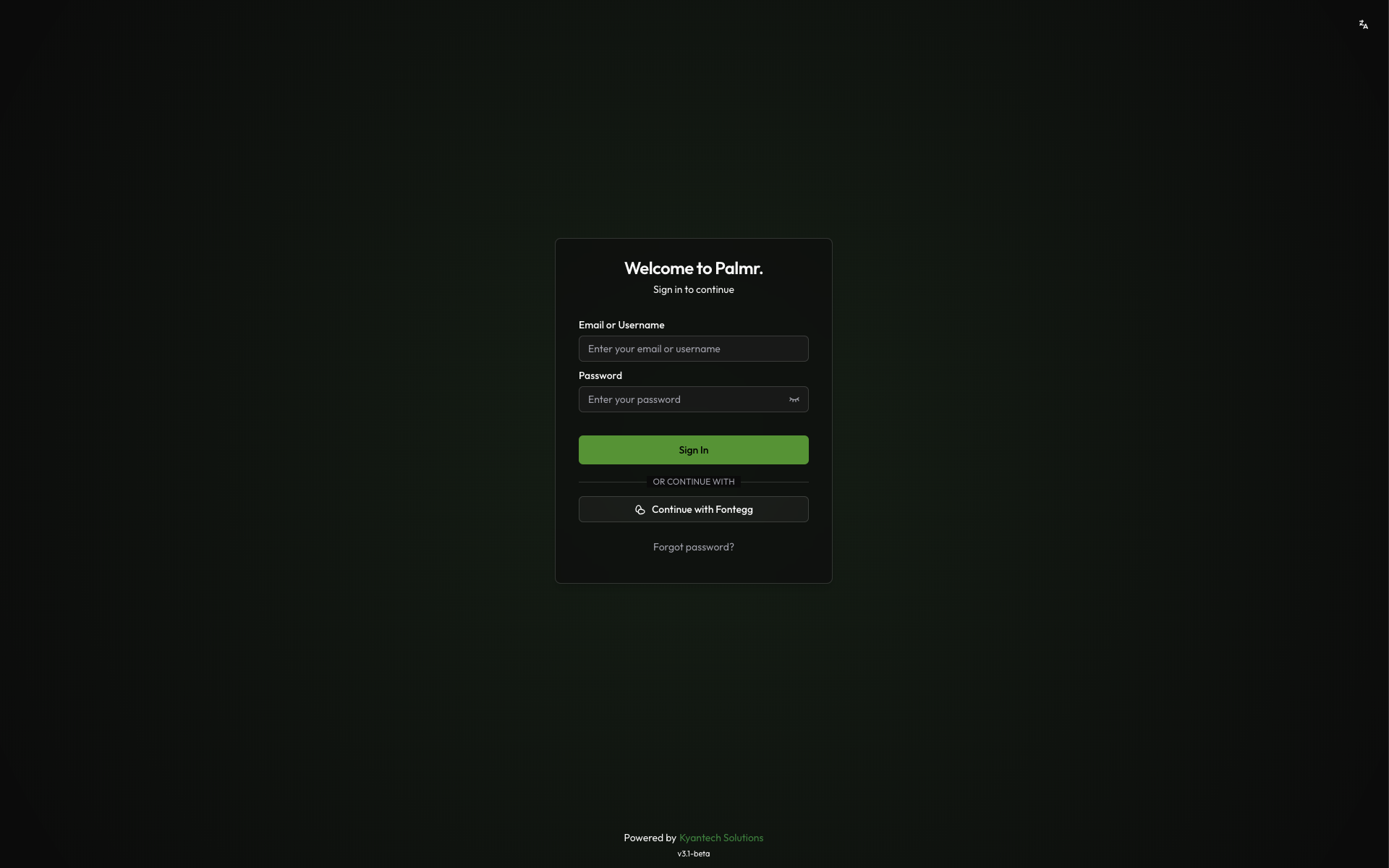
Check login page: Navigate to your Palmr login page and verify the "Sign in with Frontegg" button appears
-
Test authentication flow: Click the Frontegg sign-in button and complete the authentication process
-
Verify user creation: Confirm that a new user account is created (if auto-registration is enabled)
Login flow verification
The complete authentication process should work as follows:
- User clicks "Sign in with Frontegg": The browser redirects to Frontegg's authorization page
- User authenticates: User completes authentication through Frontegg (login, MFA, etc.)
- Frontegg redirects back to Palmr: User returns to Palmr with authentication tokens
- Palmr creates or updates user: User account is automatically managed with Frontegg information
- User accesses Palmr: User is logged in with their Frontegg identity
Troubleshooting common issues
Redirect URI mismatch error
Error message: invalid_redirect_uri
Cause: The redirect URI in your request doesn't match what's configured in Frontegg application.
Solution:
- Check the exact URL in the error message
- Add this exact URL to your Frontegg application's redirect URIs
- Ensure you include the correct protocol (http/https) and port
- Remove any trailing slashes unless they're in the callback URL
Access denied error
Error message: access_denied
Cause: User denied permissions or the application isn't properly configured.
Solution:
- Verify that your Frontegg application requests the correct scopes
- Check that users are granting permissions during the authorization flow
- Ensure your application is not restricted or disabled
- Verify the application has proper permissions set up
Invalid client error
Error message: invalid_client
Cause: Incorrect Client ID, Client Secret, or Domain.
Solution:
- Double-check that you've copied the credentials correctly from Frontegg
- Ensure there are no extra spaces or characters in the credentials
- Verify you're using the correct domain format (e.g.,
your-tenant.frontegg.com) - Generate a new Client Secret if necessary
Domain configuration issues
Error message: Domain not found or invalid
Cause: Incorrect Frontegg domain or tenant configuration.
Solution:
- Verify your Frontegg domain is correct (e.g.,
your-tenant.frontegg.com) - Check that your Frontegg tenant is active and not suspended
- Ensure you're using the correct region for your tenant
- Verify DNS resolution for your Frontegg domain
Custom claims not available
Cause: Custom claims not properly configured in Frontegg.
Solution:
- Check Frontegg custom claims configuration
- Verify that custom claims are included in the ID token
- Ensure the claims are properly formatted and accessible
- Test with a user that has the expected custom claims
Security best practices
Credential management
- Never expose secrets: Keep your Client Secret secure and never commit it to version control
- Rotate credentials regularly: Generate new Client Secrets periodically for enhanced security
- Use environment variables: Store sensitive configuration in environment variables, not config files
- Monitor access logs: Regularly review authentication logs for suspicious activity
Scope and permission management
- Minimal scopes: Only request
openid,profile, andemailscopes as required by Palmr - User consent: Ensure users understand what permissions they're granting
- Regular audits: Review which users have connected their Frontegg accounts
- Access reviews: Periodically check user access and remove inactive accounts
Production considerations
- Use HTTPS: Always use HTTPS in production environments
- Configure proper domains: Use production domains in Frontegg application settings
- Test thoroughly: Verify the complete authentication flow before going live
- Plan for failures: Have fallback authentication methods available
Next steps
With Frontegg authentication configured, you might want to:
- Configure additional providers: Set up other OIDC providers for more authentication options
- Customize user management: Fine-tune auto-registration and admin assignment rules
- Review security settings: Ensure your authentication setup meets your security requirements
- Monitor usage: Keep track of authentication patterns and user activity
For more information about OIDC authentication in Palmr, see the OIDC Authentication overview.